Convenience is a double-edged sword. When social media networks like Twitter and Facebook allow third-party services to post content on your behalf, you can utilize some pretty handy features, but the security of your social profile is reduced to the security of the third-party service. As shown in the recent Buffer hack, this often leaves users exposed to hackers who can damage your (or your business’s) credibility. Concerned about protecting your brand online? Keep reading.
What is Buffer?
![]()
Buffer (bufferapp.com) is a very useful third-party app that solves a common problem of businesses using social media. You want to post content at a steady rate, not all at once. But you don’t want to spend hours every day on Twitter and Facebook — after all, you’ve got a business to run.
Buffer provides a solution to this dilemma by allowing you to schedule your tweets and posts in advance, according to a schedule you define. That way you can spend 15 minutes queuing up your content for the day (or week) instead of having to log on every hour or so to put out your next update, hoping that you don’t forget to send something out at the right time.
The Danger
The rub is that in order to use this time-saving feature, you have to authorize Buffer to post on your behalf. This is the same with any other third-party app that posts on your behalf.
But what’s the big deal? The people at Buffer aren’t going to post anything that you didn’t tell them to, right?
True, but if the service is hacked (like the Buffer hack on Saturday) the authorization you gave to post on your behalf is now in the hands of the hackers, who typically proceed to spam as many of your followers as possible — followers you’ve worked hard to build a relationship with, followers who are potential customers for your business, followers who will probably unfollow you after receiving a spammy message.
And all the time and energy you invested in acquiring those followers is down the drain all because of a security breach.
How to Protect Your Credibility Online
There are various ways you can respond to this threat. Let’s review some, starting with the most drastic.
Don’t Use Social Media
If you don’t use social media, hackers won’t be able to commandeer your account and embarrass you in front of your (potential) customers. If your target audience isn’t on social media and/or if your brand integrity is of the utmost importance, this might be a viable solution to the threat of social media hackers.
But for many businesses, this isn’t a very good option. These days it’s almost expected that businesses have an online presence, including social media profiles. So what else can you do?
Don’t Use Any Third-Party Services
The big social networks (e.g. Twitter and Facebook) have a pretty good handle on security. Not perfect, but pretty good. Most of the social media hacks that happen now are exploits of third-party services like Buffer. If you don’t authorize any third-party services to post on your behalf, then it doesn’t matter how many hackers go after Buffer and the others; your profile will remain unscathed.
For businesses who get a big ROI from social media, this is a better solution than the first, but it still may not be ideal for you. If you don’t use Buffer, you’re back to logging on every hour or so to update your status.
Be Vigilant in Monitoring Your Profiles
If you need to be on social media and you need to use third-party services like Buffer, there’s always the possibility that your account could be hacked, but you can minimize that risk by vigilantly monitoring your social media profiles.
First of all, consider your password security. If a spammer knows your password, no hacking is required to take over your account.
Use as many kinds of characters as the service allows. If you can use both upper- and lowercase letters, use them both. If you can use numbers and special characters, use them too. Another point to keep in mind: longer passwords are better than shorter ones. It’s not a good idea to use a word found in the dictionary because hacking software can figure those out relatively quickly. However, a phrase that includes a mixture of capitalization as well as numbers and special characters could take millennia to hack. Most services these days will tell you how secure your password is as you are creating it.
Once you have your secure password, be careful who you share it with. Ideally you wouldn’t share it with anyone, but in a business setting you might have an employee handle your social media posts. If that is the case, be sure to change your password if your relationship with that employee changes. Failure to do so can have drastic consequences.
But proper password security isn’t enough to keep your accounts safe. As in the case of the Buffer hack, your password is often unnecessary in gaining access to your social media profiles. If a third-party app has authorization to post for you, a hacker can steal that authorization and post freely, just as if they were the app itself.
Because of this threat, it’s important to keep an eye on what services have authorization to use your account. To view this in Twitter, go to your settings menu and click “Apps.”
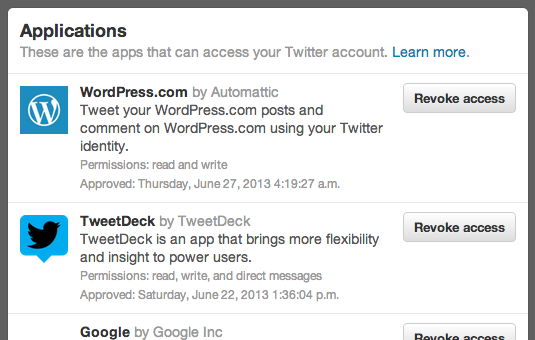
If there are any applications on the list that you don’t use anymore, go ahead and click the button to revoke access. There’s no point in leaving open a potential gap in your account’s security.
You can do the same thing on Facebook. Go to the App Center (either through the icon on the left sidebar or through your account settings) and click on “Your Apps.”
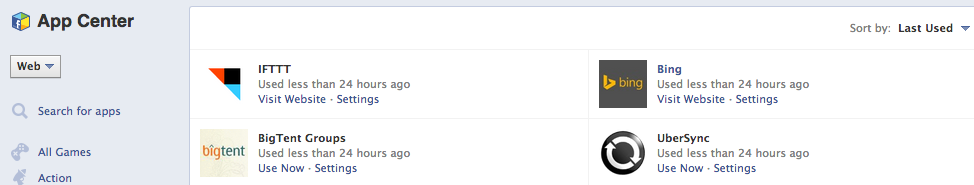
To remove apps you no longer want or use, just click the “x” in the top right corner of the app’s description.
Those precautions will prevent attacks through services that you no longer use, but what about services that you do use?
One idea is to set up notifications for every time your account publishes an update. Using services like ifttt(If This Then That) you can have an email or text sent to you whenever there’s a new post or tweet. That way if there are any nefarious updates you will be alerted immediately, allowing you to quickly remove the update and cut off the wayward app’s access to your account.
What ideas do you have? Have any ideas that I didn’t mention? Leave a comment below and share with us how you protect your brand online.
And if you need help with social media (or any other aspect of your business’s online presence) click here to contact me. For more articles about social media, security, and internet marketing, click here to follow Avid Netizen on Twitter and click here to sign up for the newsletter.
Leave a Reply